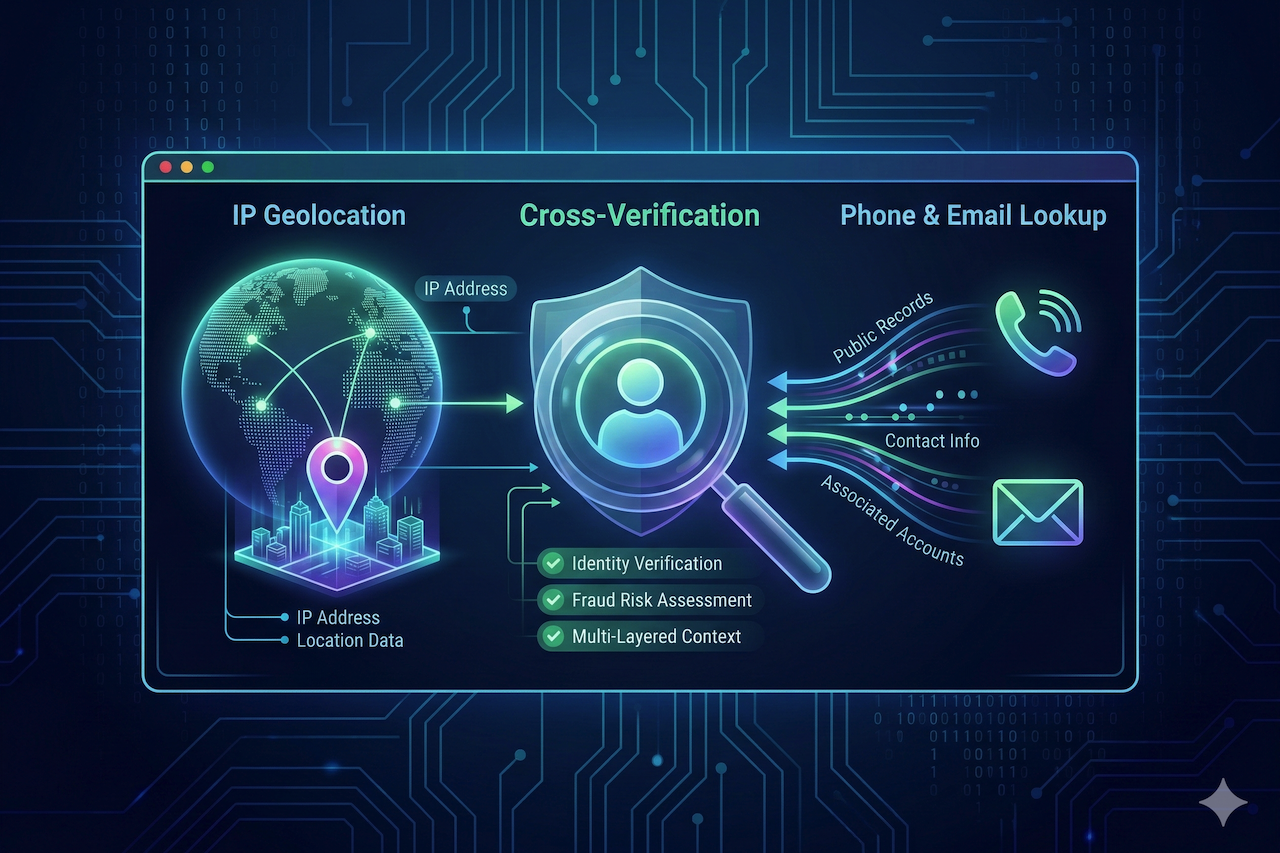
Healthcare billing fraud costs the U.S. healthcare system an estimated $100 billion every year. Behind every fraudulent claim is a chain of overlooked data signals, mismatched IP addresses, unverified provider identities, and billing patterns that fall outside normal parameters. For healthcare organizations navigating an increasingly complex billing environment, the answer may already exist in the cybersecurity tools many IT teams use daily.