Who: new hires, anyone issued a corporate device, BYOD users joining company networks, and staff after a phone is lost or returned.
Who: new hires, anyone issued a corporate device, BYOD users joining company networks, and staff after a phone is lost or returned.

In many police departments, paperwork piles up faster than anyone can keep track of it. Keeping firearms records accurate and up to date can feel like an endless chore. Modern law enforcement equipment tracking systems offer a way to manage weapons, gear, and training records without drowning in forms. These digital platforms make audits faster, accountability clearer, and daily operations smoother. By carefully embracing technology, agencies can remain compliant while protecting both officers and the public.

Here’s a practical question: when someone runs a query in your analytics platform, can every system involved still identify who that user is?
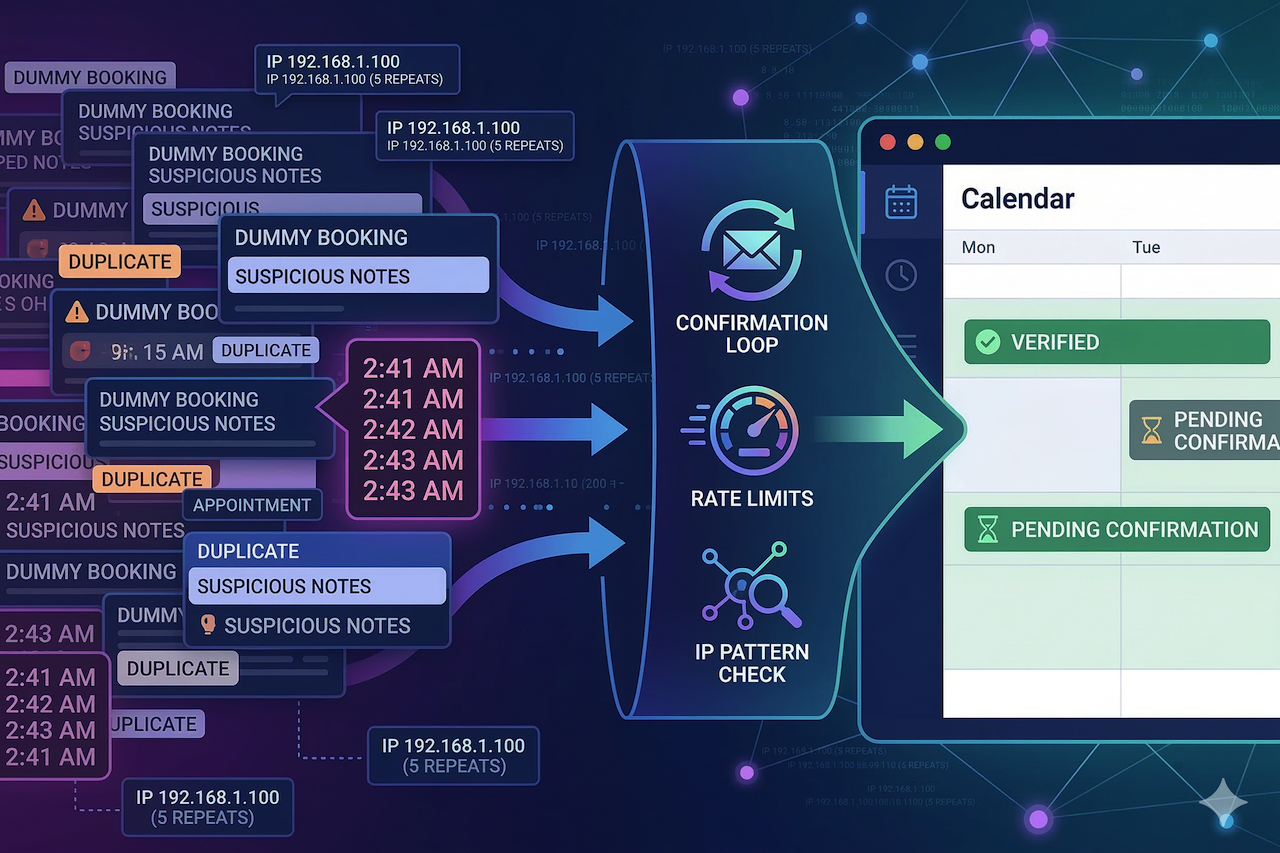
Your phone buzzes: “New booking confirmed.” Then again. And again. For a second, it feels like momentum.

Not long ago, the number of internet-connected devices in a typical home or office could be counted on one hand. A desktop computer, maybe a laptop, and a shared router formed the core of most networks. Today, that landscape has changed dramatically. Smart TVs, printers, voice assistants, cameras, thermostats, phones, tablets, and even appliances all connect to the internet, and each has its own IP address.

Political SMS outreach can win or lose voter trust in seconds. A single mistake in consent, security, or setup can lead to filtering, audits, or public backlash at the exact moment a campaign needs to reach its peak. This guide explains how campaigns can scale political SMS responsibly without sacrificing speed or effectiveness.

The answer to community-building over the last five years was, “Just create a Discord server or a channel on Telegram.” This is everything you could want as a shortcut—not to write code, not handle servers, and no development cost.

A domain name may look like a technical detail hidden behind a website, but in reality, it represents ownership, identity, and control. When access to a domain is lost, everything connected to it—email, services, reputation—can be affected at once. Because of this, modern registrars treat domain protection not as a single feature, but as a sequence of defensive layers designed to slow down, expose, and ultimately block unauthorized actions.

In today’s digital environment, protecting personal data on mobile devices has become increasingly important. Smartphones often store sensitive information such as private photos, messages, documents, and account credentials, making them attractive targets for unauthorized access. As a result, many users turn to mobile security and privacy tools to add extra layers of protection beyond default device settings.

Most people only think about the obvious travel problems. Delayed flights, lost bags, the usual. But the stuff that actually trips people up tends to be much quieter. A glitchy Wi-Fi network, an app that refuses to open because it thinks you’re someone else, or a phone that suddenly won’t receive a security code. The sort of thing you don’t even think about until you’re standing in an airport line, sweating over a login screen that worked fine at home.