In the current global landscape, cybersecurity often takes center stage. Enterprises invest millions in high-end firewalls, sophisticated encryption, and real-time IP tracking to protect their virtual assets from remote threats. However, a critical vulnerability remains in many organizational strategies: the physical office layer.
Blog Category
Have you ever wondered what happens to the important information your team shares in a personal chat app? How sure are you that your business data is secure in personal messaging apps?

Too often, online safety is viewed as a one-time thing by people. But it works better as a habit. Most break-ins still start with a human moment. Someone clicks. Someone types. Someone trusts a message that sounds close enough. Verizon’s 2024 DBIR puts the “human element” in 68% of breaches, which tells you where small changes pay off fastest.

If 2024 and 2025 proved anything, it’s that enterprise security is no longer just a perimeter problem. Attackers are moving faster, using AI more effectively, and exploiting the gaps between identity, cloud, third parties, and human behavior. That is why cybersecurity threats in 2026 looks less like a list of isolated attacks and more like a convergence of risks across the modern enterprise.

Digital document management has transitioned from local desktop applications to versatile web-based platforms. This shift offers significant convenience for remote teams and individuals who require immediate access to modification tools. However, migrating sensitive data to the cloud necessitates a rigorous approach to cybersecurity and data privacy protocols.

A flashy landing page, a ticking countdown timer, and a bright banner shouting "70% off today only" can make a platform feel legitimate in a matter of seconds. It happens to the best of us. We see a slick app store listing, a promo code shared by a creator we like, or a ticket site that pops up exactly when a major event is trending, and our brain checks a box. For many people, that is the exact moment the guard drops and the credit card comes out.

Healthcare billing fraud costs the U.S. healthcare system an estimated $100 billion every year. Behind every fraudulent claim is a chain of overlooked data signals, mismatched IP addresses, unverified provider identities, and billing patterns that fall outside normal parameters. For healthcare organizations navigating an increasingly complex billing environment, the answer may already exist in the cybersecurity tools many IT teams use daily.
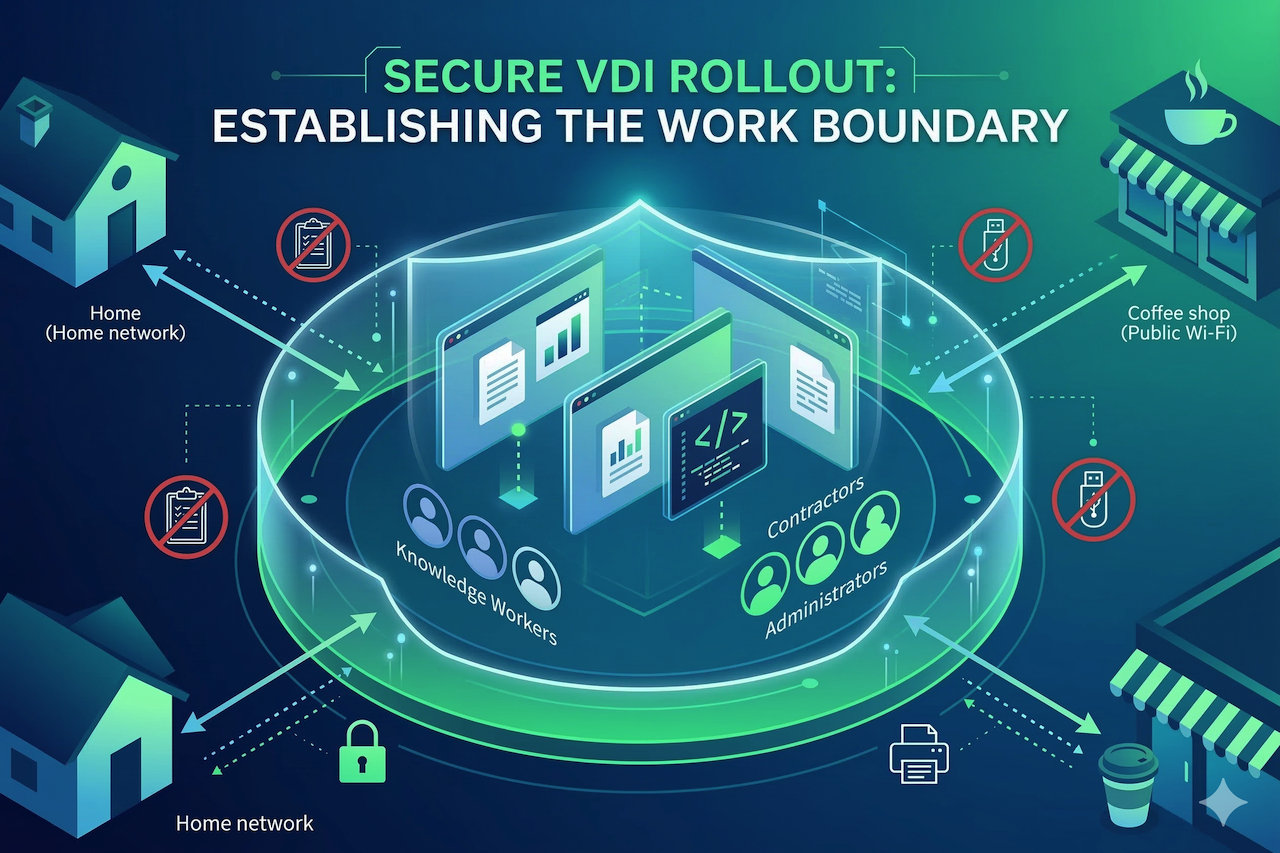
Hybrid work is now routine, and that shift changes where corporate work actually happens, across home networks, personal devices, and third-party connections. A recent OECD EU7 benchmark found that 63% of employees work remotely at least occasionally, and 43% do so weekly. In this environment, virtual desktop infrastructure (VDI) is no longer just a convenience layer but a means of enforcing consistent controls across sessions originating from inconsistent networks and devices.

Here’s a practical question: when someone runs a query in your analytics platform, can every system involved still identify who that user is?

In 2026, passwords alone are no longer enough to protect your organization. Cybercriminals are using phishing, credential stuffing, and social engineering to bypass single-factor authentication at scale making Multi-Factor Authentication (MFA) the new security baseline for businesses of every size.
