
IP intelligence used to be one of those “backend” things most teams only thought about when something broke. A bad login spike. A sudden wave of bots. A market expansion that triggered privacy questions.
In 2026, that mindset doesn’t work anymore.
IP data has become a practical layer that touches almost everything: security decisions, fraud controls, consent flows, localization, even how fast pages load for real users. And the interesting part is this: it’s not about knowing where someone is on a map. It’s about understanding what kind of traffic you’re dealing with and what you should do next.
IP context is bigger than location

Basic geolocation still has value, but it is easy to rely on it too heavily. A country or city label may appear perfectly normal, even when the underlying connection shows clear signs of risk or automation. Modern IP intelligence platforms are designed to look beyond location and answer more meaningful questions, such as:
- Is this a real residential user or a data-center hop?
- Is it a mobile carrier, corporate network, VPN provider, or a proxy pool?
- Does this IP behave like a human session or like automation?
- Is the network likely to be slow, unstable, or high latency?
Those details matter because they change the right response. Blocking by country code is blunt. Blocking by “this looks like a commercial proxy used in abuse campaigns” is sharper.
In real-world implementations, that extra layer of context can dramatically change outcomes. One financial services company originally relied on basic location rules for fraud prevention: block “high-risk” regions, allow “low-risk” regions. In practice it did two bad things at once—missed fraud coming through residential proxy networks that looked local, and blocked legitimate travelers who happened to be abroad. Once they added advanced IP intelligence (connection type, anonymization detection, historical behavior signals, plus device context), false fraud flags dropped sharply and fraud detection improved at the same time. That’s the real win: fewer angry customers and fewer losses.
Security teams can’t play whack-a-mole anymore

Attackers don’t need one IP. They can rent thousands.
Credential stuffing, scraping, and DDoS-style abuse often arrives distributed across residential proxies or compromised devices. If your defense is “block the IP after 20 failed attempts,” you’ll lose, because the attacker simply rotates.
IP intelligence helps when you stop treating IPs as isolated and start looking at patterns:
- timing that’s too consistent
- browser and session fingerprints that don’t match the story
- suspicious “human” traffic coming from infrastructure-like ranges
- clusters of behavior spread across different addresses but with the same signature
The SpdLoad team implemented this kind of detection for an e-commerce platform dealing with credential stuffing. Rate limiting wasn’t enough because the attacks were spread across thousands of “normal-looking” residential IPs. The shift that worked was detecting the shape of the attack (session behavior + IP characteristics) rather than only reacting to individual addresses. The platform blocked the majority of malicious attempts without turning login into a friction nightmare for real customers.
Compliance is where IP intelligence gets quietly essential

Privacy laws aren’t uniform. GDPR, CCPA, LGPD, and local rules keep stacking. The messy part is that obligations can change based on the user’s jurisdiction, the data’s path, and where processing happens.
A lot of companies try the “safe but heavy” approach: apply the strictest rules to everyone. It reduces legal risk, but it can also reduce product flexibility, personalization, and sometimes even growth.
Better IP intelligence lets teams be precise instead of paranoid—serve the correct consent flow, data handling, and processing route for the visitor’s jurisdiction (and log it cleanly for audits).
Situations like this are common in global products. In one case involving a global SaaS platform, SpdLoad was able to add IP intelligence layer to analyze how compliance logic was being applied across regions. The platform had initially enforced European-style restrictions worldwide, which negatively affected user experience in markets that did not require the same constraints, while still leaving gaps where local regulations differed in non-GDPR ways. By using IP-based jurisdiction detection and routing, the team was able to apply region-specific compliance logic—maintaining appropriate protections where required and removing unnecessary restrictions elsewhere. The outcome was lower regulatory risk without making the product feel universally locked down.
Personalization gets easier when you remove the annoying steps

People hate configuring basic things. Language, currency, region, shipping options. In an ideal world, the site just… gets it right.
IP intelligence improves this when it’s used carefully. It can auto-select:
- language and local formatting
- currency and regional pricing display
- inventory availability by market
- region-appropriate legal notices and consent prompts
It can also handle common edge cases like travel. A user shouldn’t be “reset” to a new experience every time they open the site from a hotel Wi-Fi. Good systems combine IP signals with session and account behavior to decide when to adapt and when to keep preferences stable.
Fraud scoring is not one signal, it’s a stack
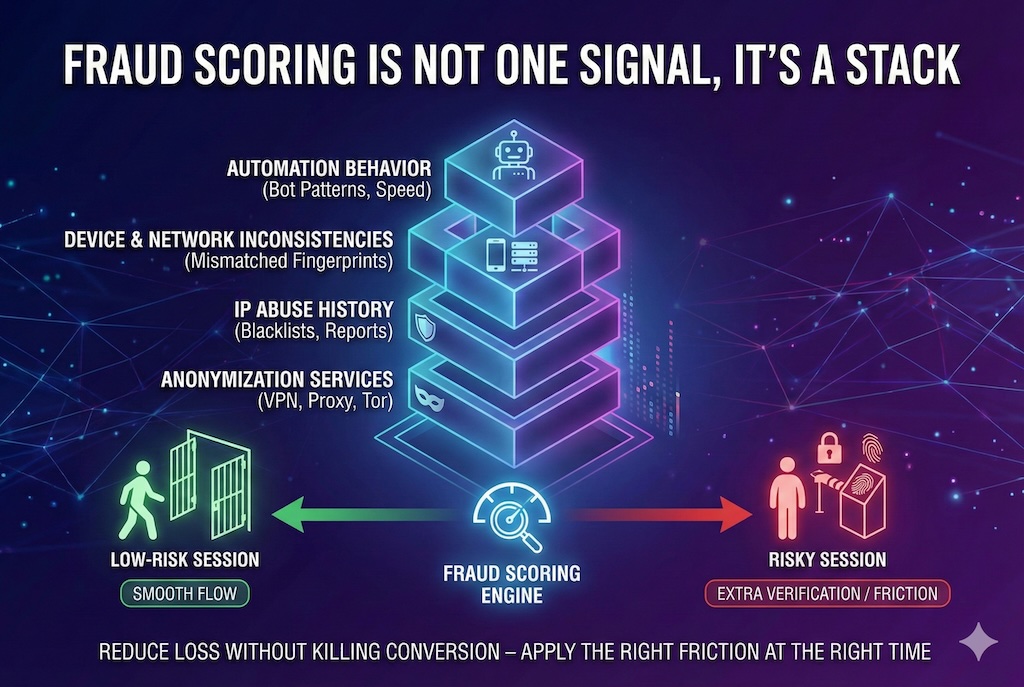
Fraud detection fails when it’s simplistic. “IP says this is New York” is not fraud prevention.
Modern scoring looks for mismatches and patterns:
- anonymization services that don’t fit the user story
- IPs tied to abuse history across multiple sources
- device and network inconsistencies
- behavior that indicates automation even when the location looks benign
The benefit isn’t just blocking more fraud. It’s applying the right friction at the right time—extra verification for risky sessions, smooth flow for low-risk users.
That balance matters because friction has a cost. The best fraud system doesn’t “catch everything.” It reduces loss without killing conversion.
Performance and routing are part of the story too
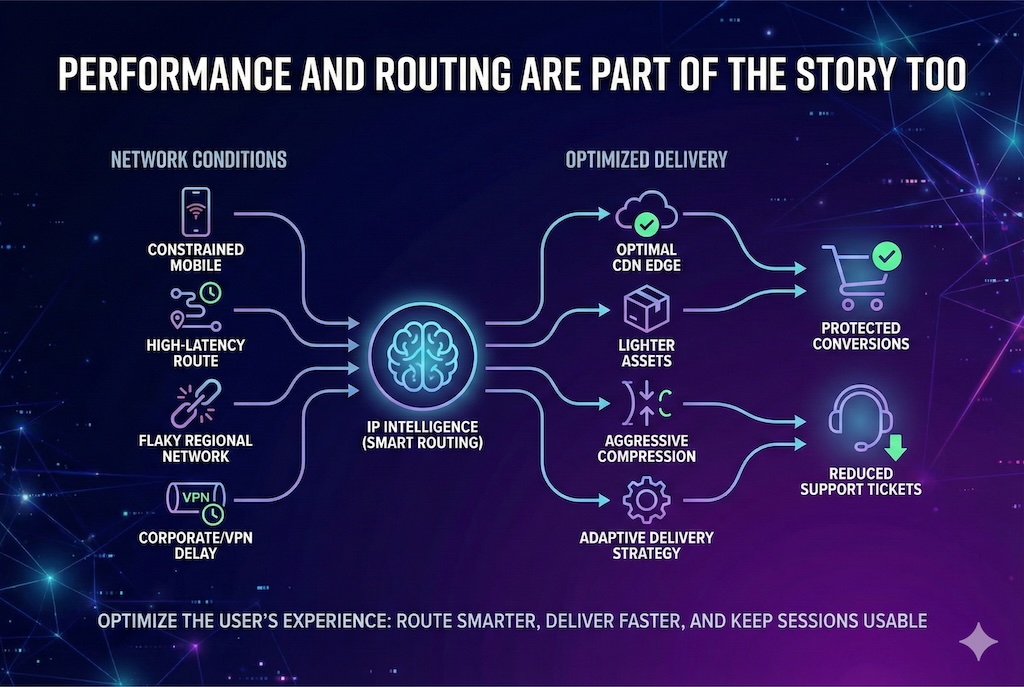
IP intelligence also helps answer a more boring but important question: How will this user’s session feel?
Network type and ISP characteristics can predict whether someone is on:
- a constrained mobile connection
- a high-latency route
- a flaky regional network
- a corporate/VPN setup that adds delay
With that, systems can route traffic to better CDN edges, serve lighter assets, compress more aggressively, or change delivery strategy so the page stays usable instead of timing out. It’s not flashy, but it protects conversions and reduces support tickets.
Account protection gets stronger with “normal vs. weird”
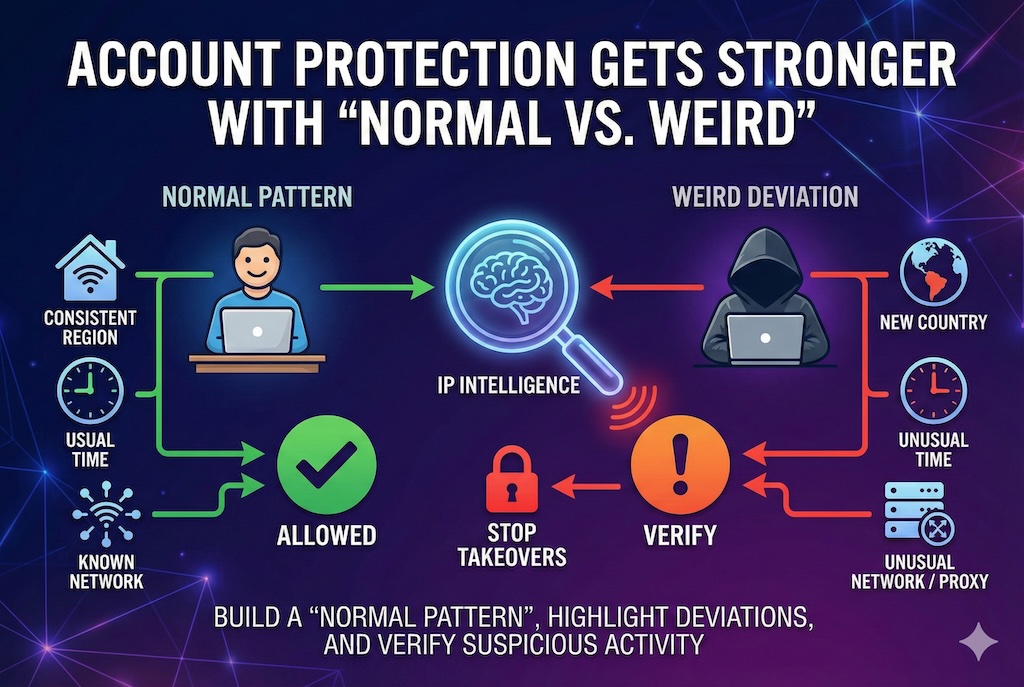
Even when credentials are valid, access can still be suspicious.
If an account that always logs in from one region suddenly appears from a new country, a new network type, or an unusual time window, you don’t need to block it outright—but you probably should verify.
This is where IP intelligence works best: it helps build a “normal pattern” for an account and then highlights deviations that are worth checking. Done right, it stops takeovers early and avoids harassing legitimate users who behave consistently.
Bots, traffic quality, and API abuse
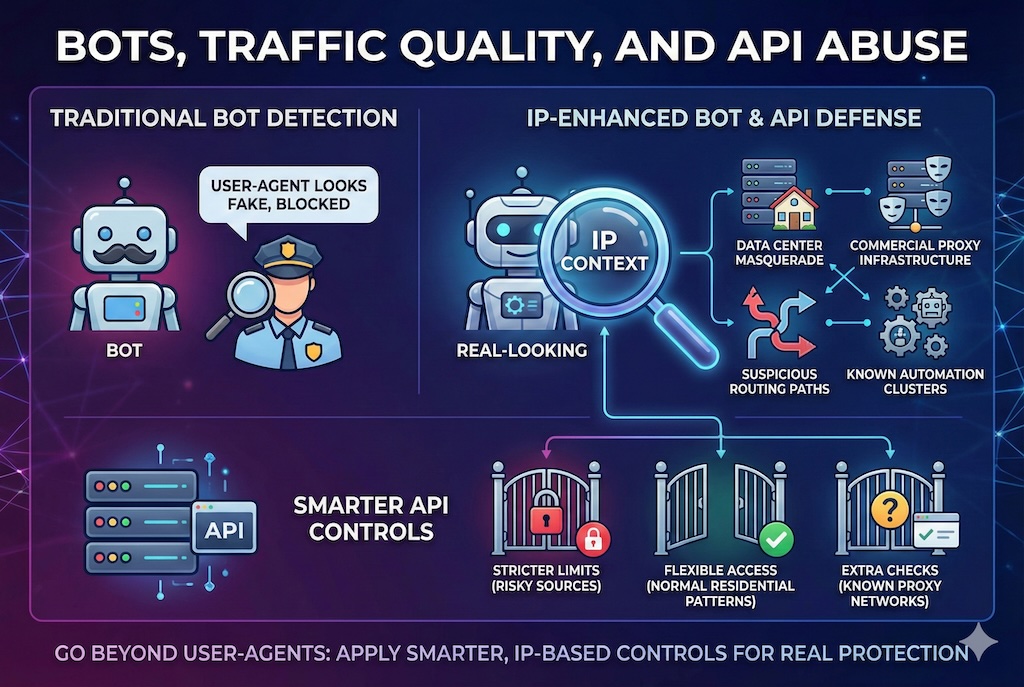
Bot detection is not just about user-agents anymore. Plenty of bots look “real.” IP context adds another layer that makes spoofing harder:
- traffic from data centers masquerading as consumers
- commercial proxy infrastructure that shows up in abuse
- suspicious routing paths
- known automation clusters
APIs benefit especially here. Simple rate limiting breaks down against distributed abuse and can hurt legitimate users behind shared networks. With IP intelligence, you can apply smarter controls: stricter limits for risky sources, more flexibility for normal residential patterns, and extra checks for known proxy networks.
IP data is also a business input
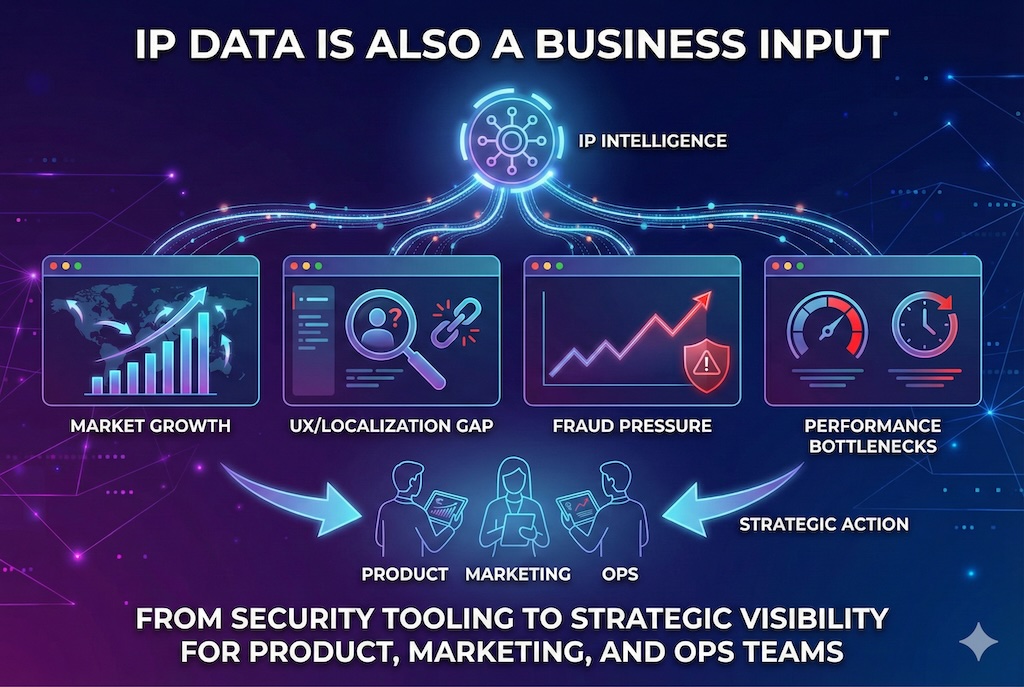
Once the operational pieces are stable, IP intelligence starts feeding strategy:
- which markets are growing
- which regions have high engagement but low conversion (often a UX/localization gap)
- where fraud pressure is increasing
- where performance is holding the product back
That kind of visibility turns IP intelligence from “security tooling” into something product, marketing, and ops can actually use.
The takeaway
In 2025, IP intelligence isn’t a niche lookup service. It’s a decision layer.
Teams that use it well:
- spot threats earlier
- reduce fraud without wrecking conversion
- handle compliance with less guesswork
- personalize without annoying setup steps
- route content for better performance globally
And because these platforms learn over time—better classifications, better threat signals, better anomaly patterns—the gap widens between organizations using comprehensive IP context and those still relying on basic location checks.
The simple rule is: if you operate globally, and you care about security, compliance, and customer experience, IP intelligence isn’t optional infrastructure anymore. It’s part of how modern systems stay reliable.
Featured Image generated by Google Gemini.
Share this post
Leave a comment
All comments are moderated. Spammy and bot submitted comments are deleted. Please submit the comments that are helpful to others, and we'll approve your comments. A comment that includes outbound link will only be approved if the content is relevant to the topic, and has some value to our readers.

Comments (0)
No comment