In the early days of the internet, a click was just a click. Today, every interaction on your network carries a massive amount of metadata. If you aren't paying attention to that data, you are likely leaving your marketing budget vulnerable. For those managing affiliate networks or large-scale digital campaigns, the shift from "growth at all costs" to "verified growth" has become the industry standard.
The reality of modern digital marketing is that as soon as there is a commission to be earned, someone is looking for a way to game the system. This isn't just about small-time hackers. We are seeing organized syndicates using sophisticated infrastructure to bleed marketing budgets dry.
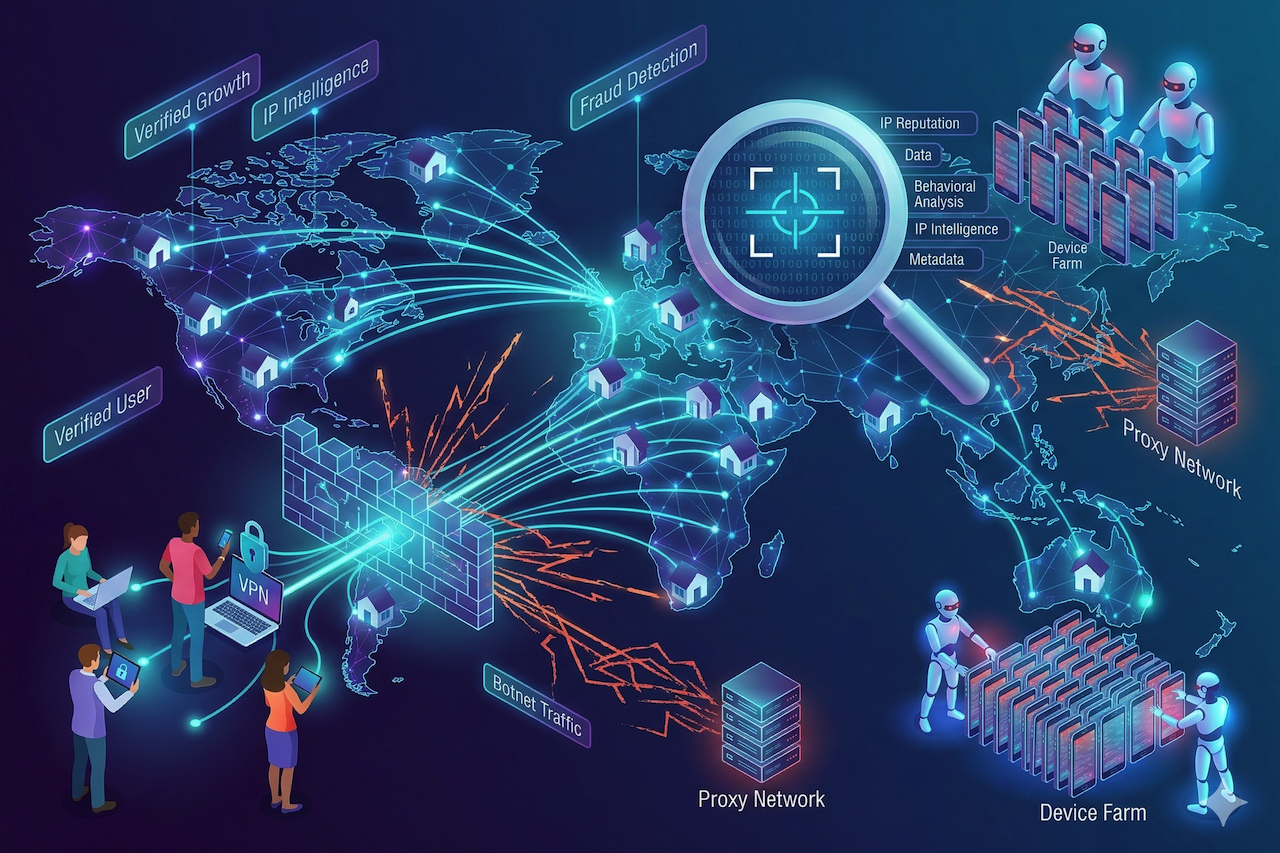
The Geography of Deception
One of the most powerful tools in your arsenal is something you likely already use for basic analytics: IP location data. While most people use it to see where their customers are coming from, savvy network admins use it to see where their fraudsters are hiding.
Data center traffic is a prime example. While a small percentage of legitimate users might browse through a VPN hosted in a data center, a sudden spike in traffic from an Amazon Web Services (AWS) IP range is a massive red flag. Real customers browse from residential ISPs like Comcast, Verizon, or BT. When your top-performing affiliate is sending 90% of their traffic from a server farm in Northern Virginia, you aren't looking at a marketing genius. You are looking at a botnet.
Why Traditional Filters Aren't Enough
Many platforms offer basic fraud protection that checks for blocked IPs. The problem? Those blocklists are outdated within minutes. Modern fraudsters use mobile proxies and residential proxy networks that route their bot traffic through real home routers and mobile devices. To a basic filter, the traffic looks like a grandmother in Ohio or a college student in London.
This is where a dedicated strategy for affiliate fraud detection becomes essential. It goes beyond checking a list of "bad" IPs. It involves analyzing the "velocity" of those IPs. If a single residential IP address is responsible for fifty different lead form submissions in an hour, that is statistically impossible behavior for a human household.
The Mobile Risk Factor
As traffic shifts toward smartphones, the complexity of tracking increases. Legitimate users often use tools to protect their privacy on public networks, such as finding the best VPN for Android to encrypt their data. However, fraudsters exploit this same technology to spoof their location.
For a network admin, the challenge is distinguishing between a privacy-conscious customer and a scammer using a VPN to bypass geo-restrictions. Advanced IP intelligence can detect "proxy headers" and identify if a user is hiding behind a known anonymous gateway, allowing you to kill the click before it ever costs you a cent.
Common Tactics Used to Exploit Networks
To stop the leak, you have to understand the methods. Fraud in the performance space usually falls into three distinct buckets:
- Cookie Stuffing: This is the digital equivalent of a pickpocket. The fraudster forces a tracking cookie onto a user’s browser without the user ever clicking an ad. If that user buys something later, the fraudster gets a "theft-based" commission.
- Lead Injection: Using headless browsers, scripts can fill out thousands of lead forms using stolen or generated data. These leads look real in your database, but are completely worthless to your sales team.
- App Install Fraud: In the mobile world, device farms use racks of physical phones to download and open apps, triggering install commissions. They use IP rotation to make it appear as if thousands of unique users are participating.
How to Build a Resilient Detection Stack
You don't need to be a coding wizard to protect your network, but you do need to be systematic. A robust defense is built in layers.
Layer 1: Pre-Click Validation
The most effective way to handle fraud is never to let it reach your landing page. By checking the IP reputation at the moment of the click, you can redirect suspicious traffic to a "404" page or a "CAPTCHA." This keeps your conversion rates clean and prevents your tracking server from being overwhelmed.
Layer 2: Behavioral Analysis
Bots are efficient, and that efficiency is their giveaway. Humans are messy. We move the mouse erratically, we scroll up and down, and we take time to read. If your affiliate fraud detection tools show that a high volume of traffic has zero dwell time or perfectly linear scrolling patterns, you can safely assume you are dealing with a script.
Layer 3: Post-Back Reconciliation
Check your data after the fact. Look for CIDR clustering. If a large chunk of your conversions is coming from the same small subnet of IP addresses, a single actor is likely running a coordinated attack on your offer.
The Bottom Line: Protecting Your Reputation
For a network or a brand, the cost of fraud isn't just the lost commission money. It is the damage to your reputation. If you are a network and you send fraudulent leads to an advertiser, that advertiser will eventually leave. If you are a brand, and your analytics are skewed by 30% bot traffic, you will make bad decisions about where to spend your next million dollars.
In the end, IP intelligence is about more than just finding a city and a state. It is about verifying human intent. By integrating deep IP data with a proactive detection approach, you move from being a target to being a fortress.
Featured Image generated by Google Gemini.
Share this post
Leave a comment
All comments are moderated. Spammy and bot submitted comments are deleted. Please submit the comments that are helpful to others, and we'll approve your comments. A comment that includes outbound link will only be approved if the content is relevant to the topic, and has some value to our readers.

Comments (0)
No comment