
Cybersecurity studies say that around 30,000 websites are hacked every day.
Many hackers break into websites without their owners realizing the issue, so it might take months before the breach is detected. At that point, making repairs is way too late.
The best protection is prevention, and this rule applies to cybersecurity. To keep a blog or author website safe from hackers, writers need to follow the best practices of cybersecurity.
In this post, we're taking a look at six essential cybersecurity practices. By the time you're done reading, you'll know how to secure your login page, data transfers, and detect potential hacking attempts before they do irreversible damage.
1. Secure Login Data
If you were a potential hacker, where would you start trying to get into a website? Of course, the WordPress login page. It's the most prominent weak point that hackers can penetrate with the so-called brute force attack - trying to log in automatically until the correct login is found.
To increase the security of the login page:
- Change the default admin name. Having admin as the username makes it 50% easier for hackers to break in. Try to avoid passwords that are similar to the name of the website (e.g. "Bradthebaker123" for bradthebaker.com). Go for something unique and difficult instead.
- Create a strong password. Use a password generator to make a super-strong password involving characters, numbers, and special symbols (don't be like those who were hacked because they had "123456" as a password).
Be wary of using a browser's autofill feature. It’s convenient, but also can make hacking really easy in case somebody gets their hands on your computer.
2. Limit Login Attempts
As you know, hackers use "brute force attacks" to break into websites. This type of cyberattacks involves using software to run up to millions of login combinations within seconds. You can stop them from attempting so by limiting the number of login attempts on your blog.
WordPress has useful plugins for that (just search for "limit login attempts" in the plugin directory). Find the one best suits your need, and get it installed.
An example Wordpress Plugin
Add such a plugin to your blog for login protection. What it does is set the number of login retry attempts (based on your choice, of course), configures lockout timing, and blocks users who exceeded their quota.
And, of course, plugins will notify you about failed attempts to log in, usually via email. So you’ll know if there’s a potential brute force attract being implemented.
3. Activate 2-Factor Authentication Where Possible
2-Factor Authentication (2FA) is a cybersecurity technique that requires website owners to enter an extra code besides the login and password when trying to sign in. The code is usually sent to a smartphone via an app or SMS message.
2FA is a strong protection method that provides evidence that the real user is trying to log in. Consider activating the same feature on your blogging platform — many of them have this feature already.
Here are some links to find 2FA onpopular platforms:
- Two-Factor Authentication for Squarespace
- WordPress plugin: Two-Factor Authentication (4.5 rating)
- Activate two-factor authentication for Tumblr
Upon activation, you’ll be required to provide the code each time you log in, so keep your smartphone with you.
4. Use a VPN for Public Wi-Fi Networks
Do you sometimes go to a coffee house or another place to write? Many bloggers and writers find it fun, and this tradition goes back centuries (they say Hemingway wrote his Paris memoir, A Moveable Feast, at a café close to his building).
Public Wi-Fi networks in many cafés and other public places are secure, but not so much in many others. It's comparably easy for a skilled hacker to access the data of other people connected to the same unprotected network.
Use VPN to keep your computer, data, and blog safe. This is something that cybersecurity professionals advise everybody who’s working in public settings because VPN hides a computer’s IP address.
What that means is that VPN keeps your browsing private by encrypting the data between you and the internet provider. No one can “see” that data, including other users of the same network, so you become invisible to potential hackers, too.
"Cybersecurity folks also recommend VPN for bloggers who pay for services online", says Nadia Lillard, a technology writer from GetGoodGrade. "This ensures payment protection in case they need to pay SEO assistants, writing experts, editors, or buy a subscription for a proofreading service."
Add a VPN and protect your blog from hacking—there are free and low-cost options readily available (ExpressVPN and NordVPN is some of the most popular ones). Even premium options cost around $10 a month, so using a VPN definitely won’t have a huge impact on your budget.
5. Install an SSL Certificate
SSL (Secure Sockets Layer) certificate is a technology that adds protection to data transferred between your blog and its visitors. This data includes emails they used to sign for your newsletter, credit card numbers for purchases, and passwords to create accounts.
Having an SSL certificate on a blog protects visitors, keeps your data transfer safe, and even helps rank higher in Google. So, it’s a must for writers and bloggers regardless of the platform they're using.
To get an SSL certificate, contact your hosting provider. Typically, certificates come as a part of hosting plans, but some might not have them. To check if your website already has an SSL certificate installed, check how its home page in a browser’s address bar.
It should have HTTPS instead of HTTP, like on Minimalist Baker, a popular cooking blog.
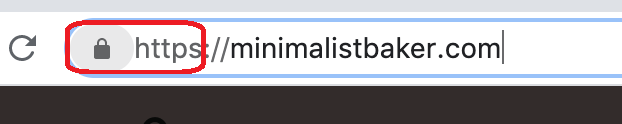
HTTPS Lock icon with https:// address
Clicking the lock symbol reveals the details about the security of the connection.
If there's a red warning or information notification circle symbol, the website's data transfer might not be secure.
6. Check Security Issues in Google Search Console
Google Search Console is a free tool that helps bloggers monitor their website's ranking and detect potential issues. Chances are you’re using it already to keep an eye on keywords and traffic, but this tool can also help with cybersecurity.
Here's how.
Google Search Console has a tab where you can check your blog for any cybersecurity-related problems. It's called "Security issues", and you can find it under "Security & Manual Actions" main menu section.
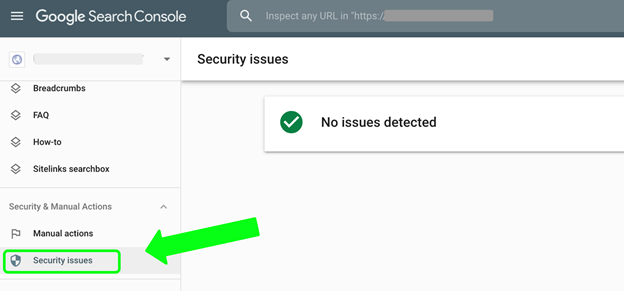
Google Search Console - Security Issues
Check the "Security Issues" tab once in a while to see if Google Search Console finds anything that can potentially compromise your blog.
Next, keywords.
You’re probably using this tool for keyword tracking to write content that converts into sales or traffic monitoring. Google Search Console shows potential and existing keywords for any page on your website, so it comes quite handy for content optimization.
But this feature can also help with cybersecurity.
One way the app can show a potential hack is through keywords your blog ranks for. If you see a strange keyword in the list of keywords a page ranks for, it might indicate that someone’s doing prohibited SEO techniques against you.
In this particular case with keywords, a hacker attempts to make your blog or website rank for keywords it wouldn't rank otherwise. For example, they can make a cooking blog rank for keywords related to clothing stores, car wash services, or other unrelated businesses.
These keywords are also clear signs of SEO spam:
- Chinese or Japanese characters
- Keywords related to illegal activities and businesses
- Unusually long keywords with 10+ words
The prohibited SEO spam technique with keywords can easily destroy a website. That’s why Google Search Console was created — to notify website owners about suspicious and prohibited activities. So, make sure to check it regularly.
Pro tip:Google search results can also show potential hacking. If the search engine result for a website has a notification saying that "This site might be hacked", it might indicate prohibited SEO methods at work.
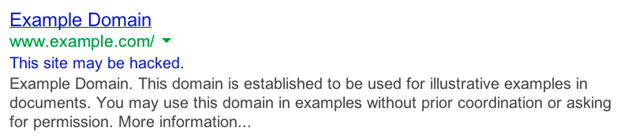
Source: Google Search Help
Google says it adds such notifications to websites where hackers might add extra pages with spam content or modify some existing pages. That's why monitoring Google Search Console and results on a regular basis is a good idea to keep a website healthy and discover problems early.
Cybersecurity for Bloggers and Writers: Summary
Nice work if you're made it this far. Now, you realize that your blog isn’t immune to cyberattacks because there are so many ways to compromise it. This realization is the first step towards creating an effective layer of protection for your content, sensitive data, and the future of your business.
Consider these six tips to nip cyberattacks in the mud. Together, they can defend your blog from thousands of cyberattacks and keep your writing business alive and thriving. But it all starts with you — unless there's a cybersecurity team working to keep your blog safe, you’re the one in charge.
Share this post
Leave a comment
All comments are moderated. Spammy and bot submitted comments are deleted. Please submit the comments that are helpful to others, and we'll approve your comments. A comment that includes outbound link will only be approved if the content is relevant to the topic, and has some value to our readers.


Comments (0)
No comment