
In a world that is becoming increasingly digital, the significance of cybersecurity cannot be overstated. As we navigate this digital era, staying one step ahead of potential threats is vital. Let's journey through the evolving landscape of cybersecurity and discover the trends that will shape our digital safety in the coming years.
In recent times, the realm of cybersecurity has transformed dramatically. As we rely increasingly on digital platforms, the need to safeguard our virtual spaces has become paramount. This article aims to shed light on poised to redefine the way we protect our digital assets in the coming years.
Let's delve deeper to understand what the future holds and how to prepare ourselves to navigate it safely.
The Current State of Cybersecurity
1. Historical Perspective
Over the years, the face of cybersecurity has undergone significant changes. From the early days of simple viruses to sophisticated cyber-attacks that can cripple entire networks, the evolution has been both fascinating and alarming. It's essential to look back and learn from the notable cyber-attacks that shook the world, understanding their impact and the measures that were put in place to prevent similar occurrences in the future.
2. The Importance of Cybersecurity Today
Today, our reliance on digital platforms is more than ever. The digital sphere encompasses a significant part of our lives, from personal data storage to business operations. This increased reliance comes with a price - the risk of cyber threats. These threats, if not managed well, can have devastating effects on individuals and businesses alike, making the role of cybersecurity not just important but indispensable.
Emerging Trends in Cybersecurity
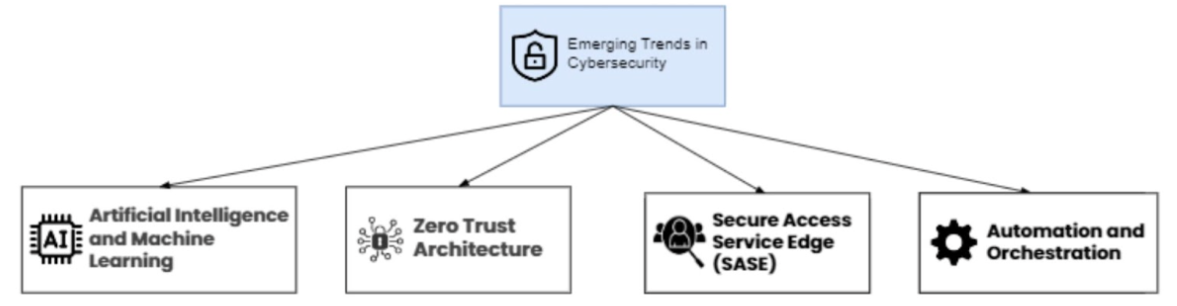
1. Artificial Intelligence and Machine Learning
As we step into the future, Artificial Intelligence (AI) and Machine Learning (ML) are set to play a pivotal role in cybersecurity. These technologies can help discover and respond to threats with a speed and accuracy beyond human capabilities. Powered by AI, predictive analytics can foresee potential threats even before they materialize, offering a new dimension to cybersecurity.
2. Zero Trust Architecture
The concept of Zero Trust Architecture is gaining ground in the cybersecurity domain. This approach operates on the principle of 'never trust, always verify,' ensuring that security is not compromised at any level. Implementing this architecture can offer a robust defense mechanism, safeguarding sensitive data and systems from potential breaches.
3. Secure Access Service Edge (SASE)
In the modern enterprise, the integration of network security with wide-area networking, known as Secure Access Service Edge, is becoming increasingly popular. This approach offers a streamlined way to protect data across the organization, fostering a safer and more secure digital environment.
4. Automation and Orchestration
In the rapidly evolving sphere of cybersecurity, automation emerges as a game-changer, promising to usher in a new era of efficiency and reliability. Minimizing reliance on human intervention significantly curtails the potential for errors that can sometimes lead to vulnerabilities. Automation facilitates the seamless orchestration of various security tools, allowing them to function synchronized. This harmony between tools streamlines the processes and fortifies the defense mechanisms, creating a robust shield against the ever-increasing and ever-sophisticated cyber threats. Thus, automation stands as a beacon of innovation, paving the way for a more secure and resilient digital landscape.
Benefits of SOAR
No doubt on what is Security Orchestration, Automation and Response (SOAR) biggest benefits is the speed and the Faster Incident Response.
The main three SOAR benefits:
- Automatisation: By automating and orchestrating processes, SOAR enables faster identification and response to threats, helping to reduce the impact of security incidents.
- Improved Efficiency: Security teams can focus on higher-level analysis and decision-making, while routine tasks are automated, leading to increased productivity.
- Consistency: SOAR ensures that incident response follows predefined, consistent workflows, minimizing human error and ensuring that incidents are handled according to best practices.
The Human Element in Cybersecurity
1. Cybersecurity Awareness and Training
As we venture further into the digital age, it becomes increasingly clear that technology, despite its advancements, cannot be the sole guardian of our cyber realms. The human factor holds undeniable significance in crafting a resilient cybersecurity infrastructure. Individuals must be well-informed and adept at recognizing and thwarting potential threats. Through comprehensive cybersecurity training and fostering a culture of awareness, employees, and users can become the first line of defense against cyber-attacks. This education, encompassing the knowledge of potential risks and the adoption of best practices, is a powerful tool in preventing the breach of our virtual sanctuaries, thereby playing a pivotal role in safeguarding our digital future.
2. The Role of Human Behavior in Cybersecurity
In the complex cybersecurity arena, gaining an insight into the mindset of cyber criminals is a crucial aspect that often goes overlooked. Understanding their motivations, tactics, and patterns can equip us with the foresight to anticipate potential breaches. Similarly, acknowledging the role of human error in cybersecurity lapses is vital. It's often the unintentional slip-ups that create openings for cyber-attacks. By focusing on the human element, both from the perspective of the attacker and the potential victim, we can craft strategies that are grounded in the realities of the cyber sector. This nuanced approach fosters a more comprehensive and effective cybersecurity strategy, one that is capable of adapting to the ever-changing tactics of cyber criminals while reducing the risks associated with human error.
Regulatory Landscape and Compliance
1. Global Cybersecurity Policies and Regulations
In the dynamic cyberspace sector, the regulatory scaffolding that governs it is in a constant state of evolution. Governments globally are taking a proactive stance in sculpting policies that delineate the standards and norms of cybersecurity, aiming to create a safer digital environment for all. These policies, often reflective of the changing nature of cyber threats, serve as a guiding beacon for individuals and organizations navigating the digital sphere. It is of paramount importance that we stay abreast of these developments, adapting our strategies and operations to the established guidelines. This ensures compliance and fosters a culture of vigilance and responsibility, which is fundamental in safeguarding our digital future.
2. Compliance Challenges
Embarking on the journey through the intricate maze of regulatory frameworks in the cyber domain can seem overwhelming at first glance. The ever-changing rules and guidelines demand a level of agility and awareness that can sometimes be challenging to maintain. With well-planned strategies and a proactive approach, navigating this landscape can be significantly simplified. It boils down to cultivating a culture of continuous learning and readiness to adapt to evolving norms. By staying knowledgeable of the latest developments and fostering a flexible approach, organizations and individuals can ensure compliance and build a robust defense against potential cyber threats, making the digital space a safer environment for all.
Future Prospects and Challenges
1. Anticipated Technological Advancements
As we stand on the cusp of a new era, our gaze fixed firmly on the horizon, we can envisage a wave of technological innovations ready to redefine the contours of cybersecurity. These advancements, brimming with the potential to fortify our digital realms, herald a future where safety and security take center stage. It is imperative to note that with innovation comes complexity, ushering in a new set of challenges that demand our attention and preparation. As we embrace the promising future, we must also equip ourselves with the knowledge and tools through the cybersecurity training to navigate the potential pitfalls, ensuring that progress leads to a more secure, and not a more vulnerable, digital landscape for future generations.
2. Building a Resilient Cyber Future
The road ahead calls for collaboration and concerted efforts to build a resilient cyber future. By fostering collaboration between governments, organizations, and individuals, we hope to create a digital space that is safe and secure for all.
Conclusion
As we wrap up, it's clear that the cybersecurity sector is in a constant state of flux. Staying vigilant and being willing to adapt to the changing trends is not just advisable but necessary. As we stand on the cusp of a new era in cybersecurity, let us embrace the changes with an informed and proactive approach.
Share this post
Leave a comment
All comments are moderated. Spammy and bot submitted comments are deleted. Please submit the comments that are helpful to others, and we'll approve your comments. A comment that includes outbound link will only be approved if the content is relevant to the topic, and has some value to our readers.

Comments (0)
No comment