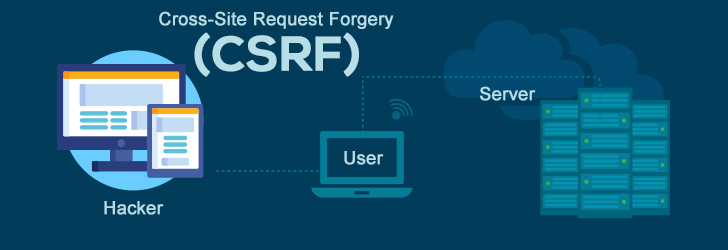
A Cross-Site Request Forgery (CSRF) is a type of attack whereby a website with malicious intent will send a request to a web application that a user is already verified for. The request is sent from a malicious website the user visits to another website which the attacker believes the user is already authenticated for. These requests are routed to the target site which the user is validated for via their browser because their browser is authenticated against the site. This means that the vulnerability for this type of attack does not lie with the website that issued the CSRF or the user but with the web application.
This will allow the attacker to access the functionality of the web application via the victim’s already authenticated browser. It is a type of attack that is frequently used against web applications that deal with social media, in-browser email clients, online banking, and web interfaces for network devices.
How it Works
The core aspect of these attacks is that the attacker is exploiting how a target web application manages authentication. This is mainly dependent on whether the user of the target web application is still logged into the web application via their browser. For example, if I visited an online banking website that had CSRF vulnerabilities and remained logged in, and another website I visited had a CRSF attack on that banking site, the attack would be executed as if I had done it myself. This means the malicious website could now take advantage of the online banking web application’s features, such as transferring funds to another account, and could potentially steal all funds on my account through an embedded code on the iframe. Once the iframe is loaded on my browser, the code will be executed by the browser and thus, the funds will be taken and the attack successful.
In addition to CSRF attacks, organizations also need to be mindful of managing user identities across different systems. This is where SCIM (System for Cross-domain Identity Management) comes into play. SCIM is a protocol designed to simplify user provisioning and management across different systems. It enables centralized identity management, making it easier for organizations to manage user accounts across various platforms and services. By implementing SCIM, organizations can ensure that user identities are properly synchronized and managed across different domains or systems.
Identifying the Vulnerability and Prevention Methods
The easiest way to identify if a web application would suffer from a CSRF attack is by checking if each form and link has an unexpected and unpredictable token attached to each user. The forms and links in question should be those that focus on state-changing functions as they are the primary targets of the attacks. On the other hand, the CSRF tokens will make it difficult for a CSRF attack to be initiated as they will be associated with each user's session. They will be, at a minimum, unique to each user’s session or request and serve the purpose of authenticating that a request is indeed valid and from a user, not a malicious website.
Conclusion
Cross-Site Request Forgery (CSRF) attacks present a stealthy yet potent threat. Exploiting how web applications handle authentication, these attacks can have severe consequences, particularly in applications dealing with critical user data like online banking and social media. The vulnerability primarily resides with the targeted web application, making it crucial to understand and implement safeguards. By incorporating unpredictable, unique CSRF tokens associated with each user's session, developers can effectively prevent these attacks. These tokens validate the authenticity of user requests, differentiating them from malicious attempts. As web applications continue to handle sensitive data, proactive measures and a solid grasp of CSRF attacks are vital to protect applications and user data, ensuring a safer online experience for all.
Share this post
Leave a comment
All comments are moderated. Spammy and bot submitted comments are deleted. Please submit the comments that are helpful to others, and we'll approve your comments. A comment that includes outbound link will only be approved if the content is relevant to the topic, and has some value to our readers.

Comments (0)
No comment