Fraud doesn’t look obvious anymore. It hides behind VPNs, residential proxies, and bot traffic that behaves like real users.
Most traditional tools miss these signals because they focus on surface-level checks rather than context.
This is where these insights helps identify hidden fraud signals behind each session.
Let’s explore the ways you can use IP intelligence to spot risk earlier and stop eCommerce fraud before it hits.
Highlights
- Fraud now hides behind VPNs, proxies, and bot traffic that look real.
- IP intelligence helps you see where traffic is coming from and what appears risky.
- It helps you spot account takeover, payment fraud, and automation early.
- Better signals mean fewer false declines and less lost revenue.
- Strong fraud prevention comes from layering IP data with other controls.
What Is IP Intelligence?
An IP address is a unique identifier assigned to a device on the internet, used by the Internet Protocol to send and receive data.
Basic IP tools show location. That’s IP geolocation.
This approach goes further.
It adds context. It analyzes IP geolocation data to detect proxies and VPNs. It also flags bot traffic and assigns risk score data based on behavior. It pulls from large IP databases to build a clearer picture of who’s really behind each request.

In other words, IP geolocation shows you where users are, and IP intelligence shows you whether you can trust them.
Why Is IP Intelligence Important?
Online shopping fraud is getting harder to spot because it no longer looks like traditional eCommerce fraud.
Attackers don’t break in. They blend in.
They use real customer data. They log in from familiar locations using VPNs or residential proxies. And they move through your site like normal shoppers.
At first glance, everything looks fine.
But underneath, a different pattern is playing out…
- Bot traffic and automation abuse are creating fake accounts, testing cards, and scraping inventory.
- Account takeover (ATO) is on the rise as stolen credentials are used to access real accounts.
- Payment fraud is slipping through checkout using valid-looking details.
- Ad fraud is draining budgets with traffic that looks real but isn’t.
The impact is significant. According to The Merchant Risk Council’s 2024 Global eCommerce Payments and Fraud Report, merchants say they lose around 3% of their total eCommerce revenue to fraud every year. They also reject roughly 6% of orders due to fraud suspicions.

Image by Google Gemini.
And this caution is valid. The Merchant Risk Council’s 2025 Global eCommerce Payments and Fraud Report shows that 98% of merchants now experience at least one major fraud attack. 26% report account takeover, specifically.
This is where IP intelligence becomes critical.
It adds real-time context to user sessions, helping you understand whether you can trust a user.
Instead of treating every login or checkout the same, you can see when something doesn’t line up.
This might show up as:
- Multiple login attempts across different IP addresses in minutes: This behavior often indicates credential stuffing or brute-force attacks.
- Traffic patterns that match bot activity, not real users: These patterns indicate scraping, inventory hoarding, or automated attacks.
- Dozens of accounts created from the same IP range: This behavior is a common sign of fake account generation or promo abuse.
- A returning customer logging in from a new country using a VPN: This could signal account takeover using stolen credentials.
- High-value orders coming from proxy or data center networks: This often links to payment fraud or reselling schemes.
- A checkout completed faster than typical human behavior: This signals automation or bot-driven purchases.
These signals give you a clear moment to act.
You can step in with the right response immediately. For instance, you might add a quick verification step, slow things down, or stop the transaction altogether.
That’s the real value of these signals.
You’re not lumping everyone together. You’re separating real customers from those exhibiting risky behavior with greater confidence. That way, you can block fraud early, while good orders complete without friction.
How Ecommerce Sites Can Use IP Intelligence to Prevent Fraud
Fraud rarely shows up as one obvious signal. It shows up as small inconsistencies.
This is where this data helps you connect the dots and act early.
1. Flag Suspicious Logins Using IP Geolocation Mismatches
Start by comparing a user’s usual behavior with their current login.
If an account that typically logs in from the U.S. suddenly appears in another country, that’s a clear signal that something may be off.
On its own, this might not confirm fraud. (The user could be traveling.) But it becomes more meaningful when paired with user behavior, device data, and session patterns.
This matters because account takeover often begins with small changes like this.
To act on it, combine IP geolocation data with device fingerprinting and login history. If multiple signals don’t align, trigger step-up authentication or block access before the user compromises the account.
2. Detect and Block Proxy and VPN Traffic
Identify users who are hiding their real location behind proxies and VPNs.
Fraudsters rely on VPN proxies and residential proxy networks to appear legitimate while masking their origin. This lets them test stolen credentials, place fraudulent orders, or bypass location-based controls without raising obvious flags.
Use IP analysis tools to identify proxy and VPN connections early.
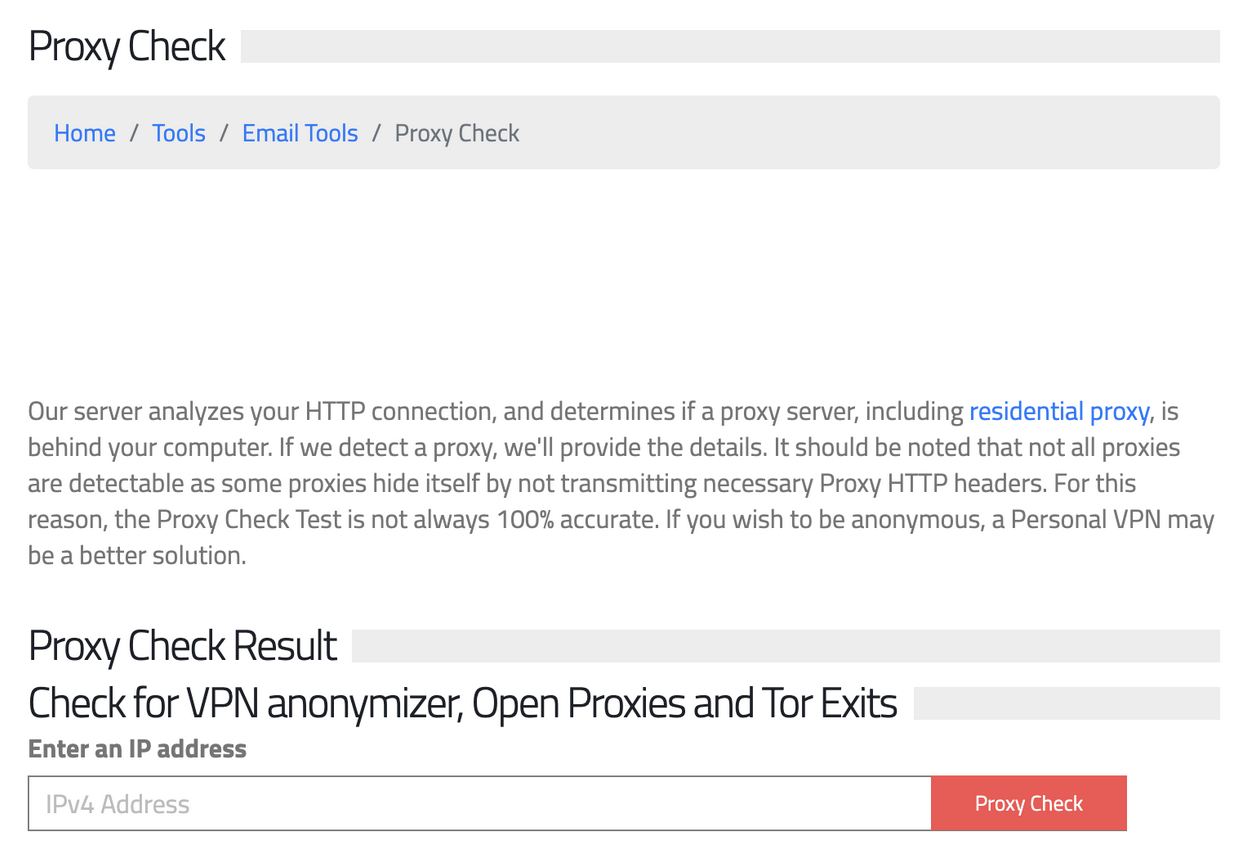
From there, apply the right response based on risk. You might add extra verification, restrict activity, or deny access altogether.
3. Identify Bot Traffic and Automation Abuse Early
Detect non-human activity before it scales.
Bot detection focuses on identifying patterns that don’t match those of real users. This often shows up as repeated actions, high-speed requests, or large volumes of traffic from the same source.
Flagging these actions helps you prevent bot networks, brute force attacks, and automated account creation.
Start by using IP data to understand where traffic is coming from.
Tools like iplocation.net help you identify unusual IP addresses, suspicious IP ranges, or traffic coming from data centers and proxy networks.
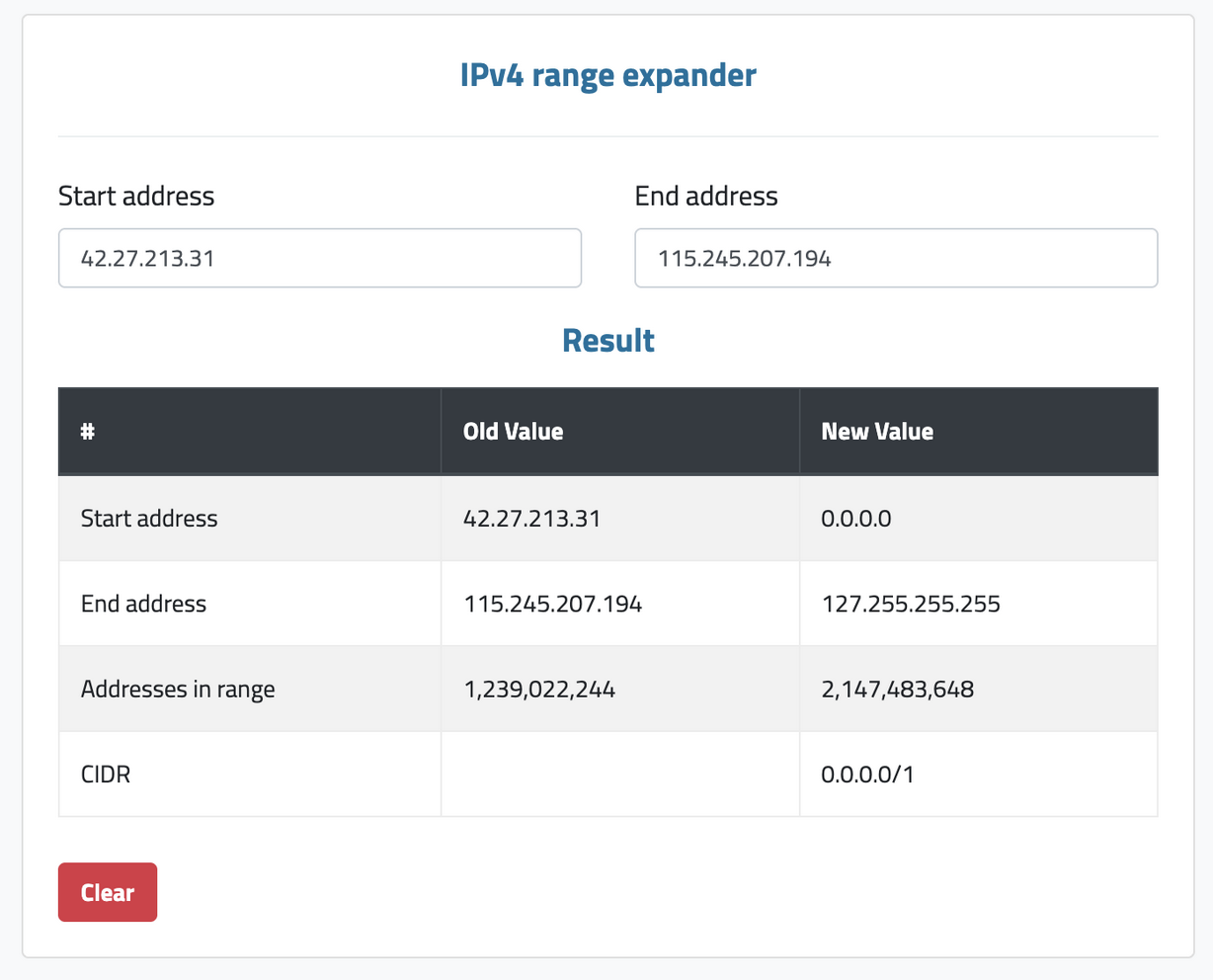
When multiple sessions share the same IP patterns or origin points, it’s often a sign of automation instead of real users.
From there, combine IP insights with simple session signals like login frequency or checkout speed. If the activity looks automated, you can step in to block the user.
4. Use Risk Scoring to Protect Checkout and Payments
Assess the risk of each transaction using multiple signals. Look at the details.
Risk scoring works by identifying mismatches across a data stack.
That includes IP intelligence, anonymization signals like VPNs and proxies, IP abuse history, device and network consistency, and session behavior. A location alone doesn’t tell you much. What matters is whether the full picture makes sense.
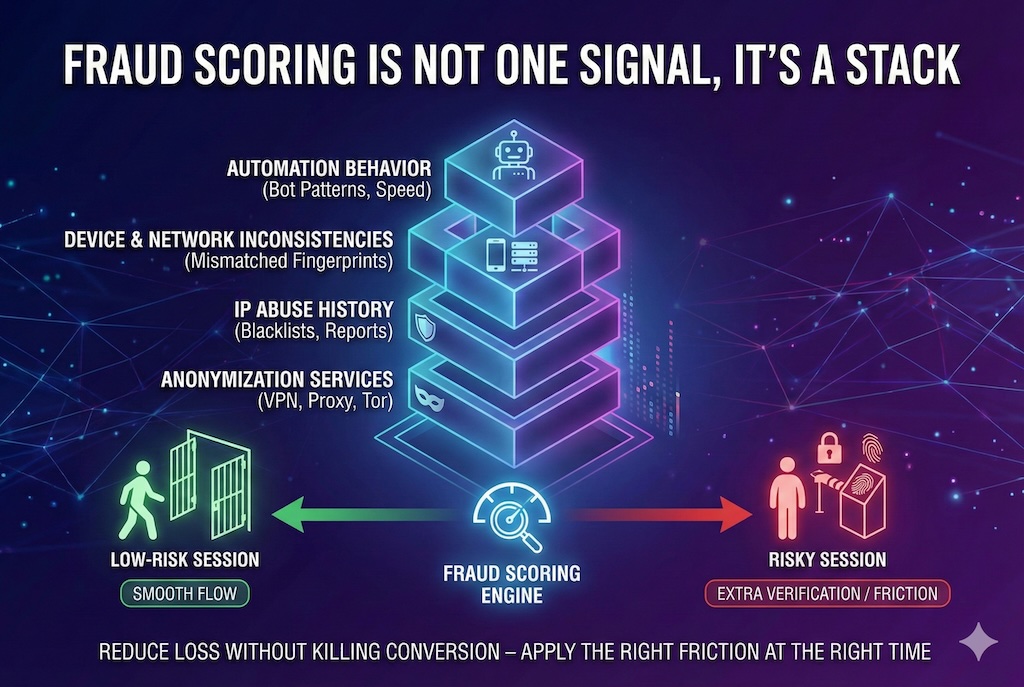
These tools help you understand where traffic originates and whether an IP raises concerns. You can then combine this with your own session and user data to assess risk.
When signals align, this shows the user is legitimate. When they don’t, increase friction to block fraudsters.
5. Combine IP Intelligence with Application-Level Security
Go beyond identifying risky traffic and control what can actually run inside your environment.
While IP-based signals helps you spot suspicious access, it doesn’t stop what happens next if someone gets through.
This is where application allowlisting helps.
Application whitelisting ensures that only approved scripts and software can run across your systems, including checkout and payment flows.
This is important because many fraudsters inject malicious code, intercept transactions, or manipulate processes after gaining access.
By locking down what can execute, you reduce the chances of fraud, even if you miss the initial signals.
6. Strengthen Your Infrastructure with Vulnerability Management
Close the gaps attackers look for.
These signals are great for spotting risky traffic. But if your systems aren’t secure, attackers can still get in. That’s where vulnerability management comes in.
Regularly patch software, secure your APIs, and fix known weaknesses so online attacks can’t bypass your defenses.
This protects customer data and ensures your fraud controls hold up in real-world scenarios.
7. Build a Layered Defense with AI-Driven Security
Don’t put all of your trust in one signal. Build multiple layers of protection.
Fraud tactics change fast, and attackers adapt just as quickly.
Working with an AI cybersecurity company helps you stay ahead as fraud evolves.
These experts will help you add behavioral detection, real-time response, and employee awareness to catch threats earlier.
When you layer these signals together, you create a stronger security ecosystem that can keep up with evolving fraud tactics.
Wrap Up
Fraud is evolving, and it’s getting harder to spot.
This is why this approach matters.
IP intelligence gives you early visibility into where web visitors come from, how they behave, and what doesn’t add up. This helps you catch risks before they turn into financial losses.
 FAQs
FAQs
IP intelligence uses IP address data to understand where users come from and whether their activity looks risky. It identifies signals such as unusual locations, proxy or VPN usage, and behavior patterns that don’t match typical user activity.
This approach can detect many VPNs and proxies by analyzing IP ranges, hosting providers, and known anonymization networks. However, advanced tools such as residential proxies are harder to identify because they mimic real users. For best results, IP data should be combined with behavioral and session-based signals.
When implemented correctly, IP insights enhance the user experience by identifying risky activity without blocking legitimate users or introducing unnecessary friction during login or checkout.
Featured Image generated by ChatGPT.
Share this post
Leave a comment
All comments are moderated. Spammy and bot submitted comments are deleted. Please submit the comments that are helpful to others, and we'll approve your comments. A comment that includes outbound link will only be approved if the content is relevant to the topic, and has some value to our readers.

Comments (0)
No comment