When a request hits a server, the platform doesn’t just see an IP address - it considers a fingerprint. That fingerprint tells a story about where the connection came from, what network owns it, and whether it behaves like a human or a script. Understanding these detection mechanics doesn’t just explain why some connections get blocked. It reveals the structural advantages certain IP types have - advantages that can’t be patched away with better code or smarter rotation.
TL;DR:
- Datacenter IPs get flagged instantly via ASN lookup, no behavioral trick saves them
- Residential IPs pass classification but often fail reputation checks due to industry-wide contamination
- Mobile IPs have structural immunity
- CGNAT means blocking one IP blocks thousands of legitimate users
- This advantage isn’t a loophole; it’s how carrier networks are built
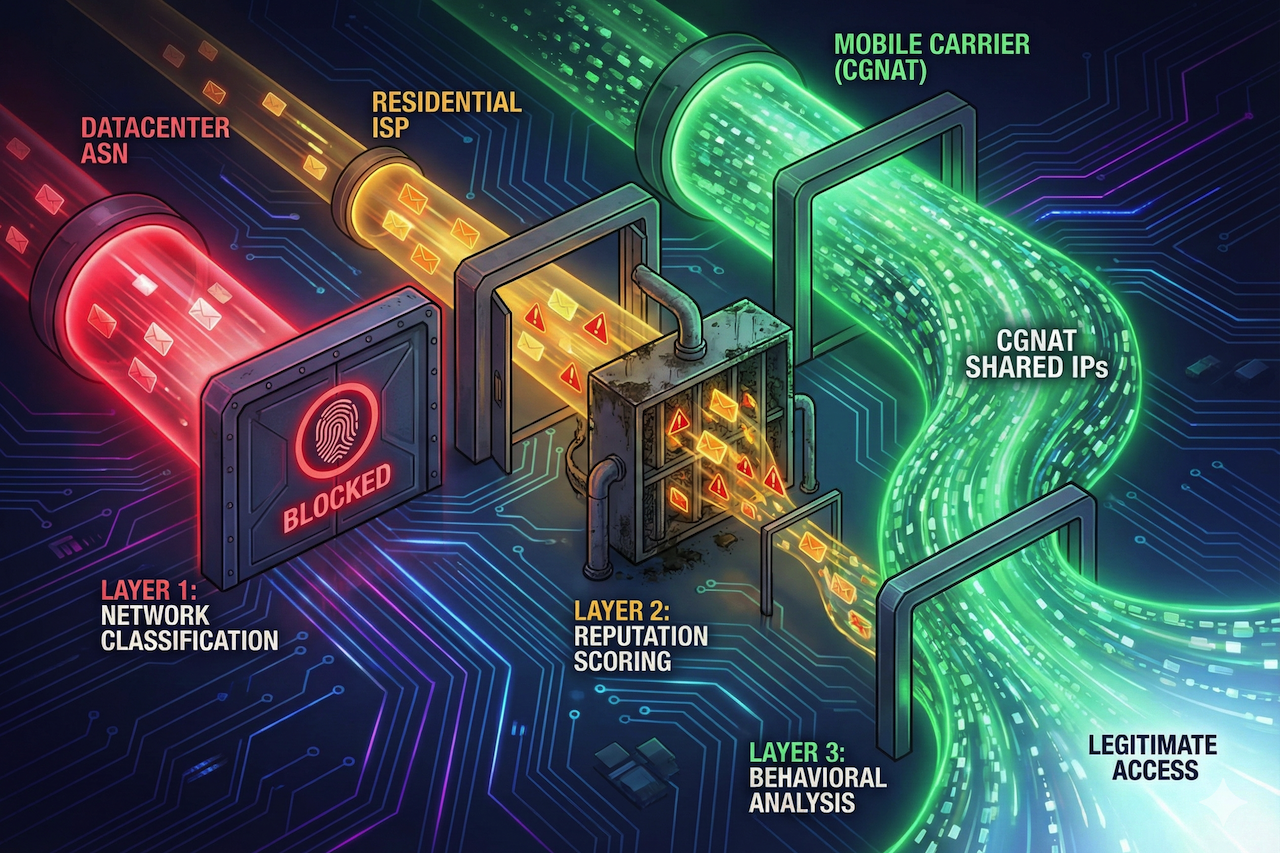
The Detection Stack
Modern platforms layer three systems on top of each other:
Layer 1: Network Classification
Before your first byte of content loads, the platform already knows whether you’re connecting from a datacenter, a home ISP, or a mobile carrier. This classification happens through ASN (Autonomous System Number) lookups against maintained databases.
Layer 2: Reputation Scoring
Every IP carries historical baggage. Has this address been associated with spam, abuse reports, or known proxy traffic? This reputation score adjusts how strictly the platform evaluates your session.
Layer 3: Behavioral Analysis
How does the session unfold? Request timing, mouse patterns, scroll behavior, and JavaScript execution all factor in. Even identical actions are scored differently depending on what Layers 1 and 2 have already revealed.
The key insight: these layers multiply, not add. A datacenter IP starts with a penalty that makes Layer 3 nearly impossible to pass. A mobile IP starts with a bonus that makes Layer 3 almost irrelevant.
Why Datacenter IPs Fail Before You Even Try
Datacenter IP ranges are public knowledge. AWS, Google Cloud, OVH, Hetzner, DigitalOcean - their ASN blocks are documented and maintained in databases that every major platform queries.
When traffic arrives from a known datacenter ASN, the platform makes a reasonable assumption: regular users don’t browse from AWS. This isn’t a bug in detection; it’s working as intended.
No amount of behavioral mimicry overcomes this. You can randomize timing, simulate mouse movements, and rotate user agents, but the ASN lookup already happened. The session is flagged before your carefully crafted behavior even gets evaluated.
This is why datacenter proxies tend compete on price rather than quality. The fundamental constraint isn’t their infrastructure; it’s the public classification of their IP ranges.
The Residential Trap
Residential IPs seem like the obvious solution. They resolve to consumer ISPs - Comcast, AT&T, BT - networks that serve real households. The ASN lookup returns “residential,” and the session starts with legitimate classification.
But there’s a second-order problem: the proxy industry has poisoned the well.
For years, large volumes of residential IPs have been sourced through questionable methods - browser extensions with buried consent, “free VPN” apps that sell user bandwidth, P2P networks where users don’t realize they’re exit nodes. These IPs are used across hundreds of services, accumulate abuse reports, and build a negative reputation.
The result: a residential IP might pass Layer 1 (network classification) but fail Layer 2 (reputation). The ASN says “home user,” but the IP’s history says “proxy traffic.”
Higher-quality residential IP pools tend to maintain cleaner reputations through stricter sourcing controls and faster removal of flagged addresses. However, these IPs typically come at a significantly higher cost, and even then, they remain affected by broader industry-wide reputation contamination.
The Mobile Structural Advantage
Mobile IPs work differently, not because of service quality, but because of how carrier networks are architected. Mobile networks use Carrier-Grade NAT (CGNAT). Unlike residential connections, where each household receives a unique public IP address, mobile networks assign the same public IP to thousands of devices simultaneously. A single carrier IP may serve hundreds of phones within the same city at any given moment.
This creates a detection problem that platforms can’t solve: blocking mobile IP addresses blocks legitimate customers. Not one customer, potentially thousands who happen to share that address.
The math doesn’t work for aggressive filtering. A platform that blocks datacenter ranges loses almost no legitimate users. A platform that blocks mobile carrier ranges loses significant revenue and generates support tickets from real customers wondering why they can’t access the service.
This isn’t a loophole that detection systems will eventually close. It’s a structural feature of how mobile networks operate. Carriers have no incentive to change it. CGNAT saves them expensive IPv4 addresses.
The shared nature of mobile IPs provides inherent protection that datacenter and residential IPs don’t. Some mobile proxy services, such as VoidMob, operate by routing traffic through real 4G and 5G carrier infrastructure rather than relying on emulated or hosted network environments.
What Actually Gets Flagged (Even With Good IPs)
Having a trusted IP type is necessary but not sufficient. Sessions still get flagged for behavioral signals that don’t match human patterns:
- Timing consistency: Real user behavior includes variable delays between actions. Scripts often have suspiciously consistent timing, even with random delays added. The variance pattern matters as much as the delays themselves.
- Session coherence: Humans browse in connected ways. They click a link, read the page, and then click another related link. Sessions that jump between unrelated pages without apparent logic trigger suspicion.
- Capability mismatches: Headers may claim Chrome on Windows, but JavaScript execution reveals something else, or the reported timezone doesn’t match the IP’s geographic location. These mismatches are easy to create accidentally and hard to debug.
- Request patterns: Accessing the same resource repeatedly, hitting endpoints in mechanical sequences, or making requests faster than a human could realistically read responses.
The platforms aren’t looking for any single signal. They’re looking for combinations that diverge from baseline human behavior. Mobile IPs give you more tolerance for deviation, but they don’t provide you with immunity.
Why Detection Arms Races Favor Mobile Infrastructure
Detection systems constantly evolve. Platforms share intelligence, update databases, and refine behavioral models. What worked last year might not work today.
But the mobile advantage is structural, not tactical. It doesn’t depend on being ahead of detection updates. It depends on the carrier network architecture that platforms can’t change.
Datacenter detection improves over time because the ASN databases become more complete. Residential detection improves because reputation tracking becomes more sophisticated. The CGNAT problem caps mobile detection: Shared IPs mean aggressive filtering causes unacceptable collateral damage.
This is why mobile proxy infrastructure requires fundamentally different architecture than datacenter or residential services. The trust comes from the carrier relationship, not from IP acquisition.
Choosing Based on Detection Risk
The decision framework becomes straightforward once you understand the detection stack:
- Unprotected targets: Datacenter is fine. Small sites, internal tools, APIs without bot protection. No reason to pay more when Layer 1 filtering doesn’t exist.
- Moderate protection: Residential IPs can work, but quality matters enormously. Lower-quality pools with contaminated reputations fail at Layer 2, while cleaner, well-managed IP pools pass more consistently.
- Aggressive protection: Mobile is the reliable choice. Social platforms, financial services, and e-commerce with sophisticated bot detection. The structural advantage of CGNAT provides tolerance that other IP types can’t match.
- Account-based work: Mobile is nearly mandatory. Login flows, session persistence, and actions that accumulate trust over time. The combination of high initial trust and natural IP rotation (carriers reassign addresses frequently) creates sustainable sessions that other IP types struggle to maintain.
The Underlying Reality
Detection systems aren’t trying to block proxies. They’re trying to block automated abuse while allowing legitimate users through. Mobile IPs pass because they’re indistinguishable from legitimate mobile users because they are legitimate mobile connections, just routed through infrastructure.
This is the fundamental insight that separates practical approaches from endless arms races: you’re not trying to evade detection, you’re trying to be genuinely indistinguishable from what the traffic platforms want to allow.
Conclusion
Modern detection systems evaluate far more than individual requests. Network classification, IP reputation, and behavioral analysis combine to determine whether traffic is trusted or blocked. While tactics and tooling continue to evolve, structural factors such as carrier network design create lasting differences between IP types.
The platforms will keep improving detection, and carriers will continue using CGNAT. As long as both of those realities hold, the structural advantage of mobile IPs will remain intact.
Understanding these mechanics allows teams to choose infrastructure based on detection risk rather than trial and error. In practice, the most sustainable approaches align closely with how legitimate users access platforms, rather than attempting to outsmart detection systems through short-term workarounds.
 FAQs
FAQs
No. The ASN lookup happens before any behavioral analysis. The classification is baked into the IP range itself, and no amount of fingerprint spoofing or request timing adjustments can change that.
Lower-quality residential IP pools often accumulate abuse reports over time. While the ASN may indicate a residential network, the IP’s history reflects repeated proxy-related activity.
Individual IPs can accumulate negative signals, but carriers rotate them frequently. The structural protection provided by CGNAT means platforms cannot block aggressively without impacting large numbers of legitimate users.
Carrier-Grade NAT enables mobile carriers to assign the same public IP address to thousands of devices simultaneously. Blocking a single IP would therefore block thousands of legitimate users, which platforms are generally unwilling to do.
As long as carriers continue using CGNAT and platforms cannot afford to block large volumes of legitimate mobile users, the structural advantage remains. This is not a loophole but a consequence of how mobile network infrastructure is designed.
Comparative proxy performance data can be found in independent testing reports, technical benchmarks, and published research materials. Some services publish a mobile proxy comparison guide that outlines differences between mobile, datacenter, and residential IP types. VoidMob’s mobile proxy comparison guide is one example of this type of reference material.
Featured Image generated by Google Gemini.
Share this post
Leave a comment
All comments are moderated. Spammy and bot submitted comments are deleted. Please submit the comments that are helpful to others, and we'll approve your comments. A comment that includes outbound link will only be approved if the content is relevant to the topic, and has some value to our readers.








Comments (0)
No comment